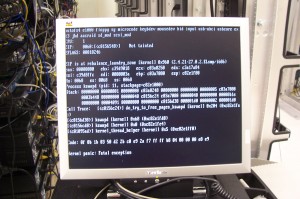
Linux has developed a new way to track kernel panic errors. OPW Intern Teodora Băluţă spent her three-month internship this year designing a program to capture and send Linux kernel crash and error messages, called oops, as QR codes. To capture oops as QR codes, Băluţă first had to research existing QR code libraries that were compatible with the kernel and could also handle a large amount of text. She also studied algorithms capable of compressing all of that data and ended up using the zlib inside the kernel code. Finally, she had to insert hooks into the various oops paths in the kernel to catch the outgoing messages that comprise the full oops message.
Kernel developers use oops to find and fix programming errors that cause problems in the Linux kernel. Compressing them into QR codes solves several problems with this process, said PJ Waskiewicz, the Linux kernel developer who mentored Băluţă’s internship with Intel, funded by The Linux Foundation. For example, he said, “if I’m working on my laptop while traveling, and hit some obscure bug that I only see once every 3-4 months, I want to make sure to get a clean capture of the panic. I don’t have a serial console hooked up, I may be running some graphics workload that hangs the display, so the panic may have dumped the backtrace, but there’s no way to extract it. A QR code can encapsulate an entire oops and will still always fit on screen. Using KMS (kernel mode setting), it can also write the QR code to a portion of the framebuffer that will always be visible, so you never lose the panic”, Waskiewicz said. And in a QR code format, you don’t need to be a kernel developer to find, read and report an oops – just take a picture of the crash and send it to your favorite bug reporting software so a kernel developer can dig into it.
Though her internship ended in March, Teodora is continuing with development of an Android app that will help process the kernel panic trace by taking a photo of the QR code, decoding it, and reporting it to a central database, such as bugzilla.kernel.org or kerneloops.org.
Source: linux.com